AES256 加密解密 Encryption in SAP ABAP

DATA: lv_plaintext TYPE string,
lv_xplaintext TYPE xstring,
lv_key TYPE string,
lv_xkey TYPE xstring.
DATA: lv_iv TYPE string,
lv_xiv TYPE xstring.
DATA: lv_len TYPE i.
DATA: lv_ciphertext TYPE string,
lv_xciphertext TYPE xstring.
DATA: lv_msg TYPE string.
SELECTION-SCREEN BEGIN OF BLOCK blk1 WITH FRAME TITLE TEXT-t01.
PARAMETERS: p_ptext TYPE string LOWER CASE OBLIGATORY DEFAULT 'This is Plaintext 这是明文 Fake News',
p_iv TYPE string LOWER CASE OBLIGATORY DEFAULT '0000000000000000',
p_key TYPE string LOWER CASE DEFAULT 'AESEncryptionKey'.
SELECTION-SCREEN END OF BLOCK blk1.
INITIALIZATION.
START-OF-SELECTION.
WRITE:/ p_ptext,
/ p_key,
/ p_iv.
ULINE.
PERFORM frm_to_xstring USING p_ptext 'UTF-8' CHANGING lv_xplaintext.
PERFORM frm_to_xstring USING p_key 'UTF-8' CHANGING lv_xkey.
IF p_iv IS INITIAL.
lv_iv = '00000000000000000000000000000000'.
ELSE.
lv_iv = p_iv.
ENDIF.
lv_len = strlen( p_iv ).
PERFORM frm_to_xstring USING lv_iv 'UTF-8' CHANGING lv_xiv.
WRITE:/ lv_xplaintext,
/ lv_xkey,
/ lv_xiv.
ULINE.
IF p_key IS INITIAL.
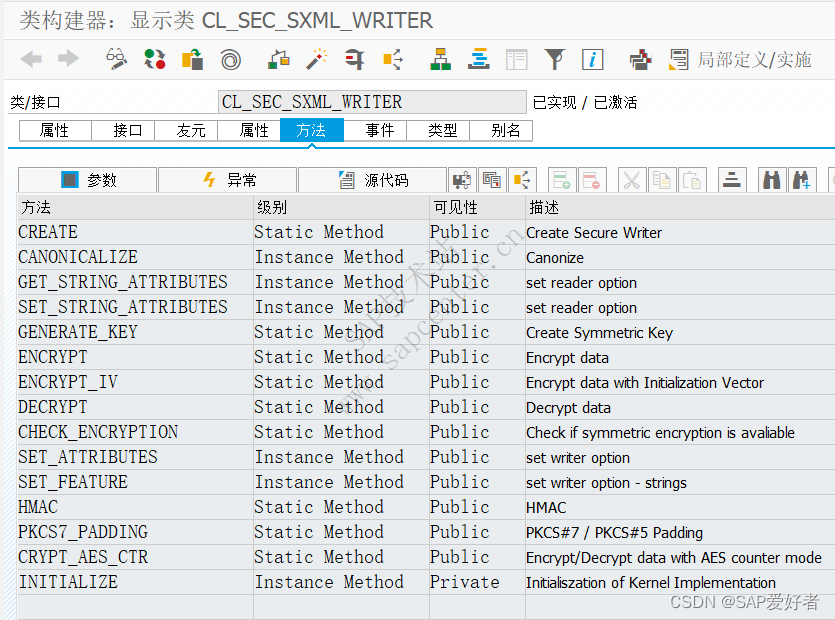
CALL METHOD cl_sec_sxml_writer=>generate_key
EXPORTING
algorithm = cl_sec_sxml_writer=>co_aes256_algorithm_pem
RECEIVING
key = lv_xkey.
ENDIF.
TRY.
CALL METHOD cl_sec_sxml_writer=>encrypt_iv
EXPORTING
plaintext = lv_xplaintext
key = lv_xkey
iv = lv_xiv
algorithm = cl_sec_sxml_writer=>co_aes256_algorithm_pem
IMPORTING
ciphertext = lv_xciphertext.
WRITE:/ lv_xciphertext.
lv_xciphertext = lv_xciphertext+lv_len.
PERFORM frm_base64encode USING lv_xciphertext CHANGING lv_ciphertext.
WRITE:/ lv_ciphertext.
CONCATENATE lv_xiv lv_xciphertext INTO lv_xciphertext IN BYTE MODE.
CLEAR: lv_xplaintext.
CALL METHOD cl_sec_sxml_writer=>decrypt
EXPORTING
ciphertext = lv_xciphertext
key = lv_xkey
algorithm = cl_sec_sxml_writer=>co_aes256_algorithm_pem
IMPORTING
plaintext = lv_xplaintext.
WRITE:/ lv_plaintext.
CATCH cx_sec_sxml_encrypt_error INTO DATA(lo_sec).
lv_msg = lo_sec->get_text( ).
WRITE:/ lv_msg.
ENDTRY.
PERFORM frm_to_string USING lv_xplaintext 'UTF-8' CHANGING lv_plaintext.
WRITE:/ lv_plaintext.
FORM frm_to_string USING lv_in
lv_encoding
CHANGING lv_out.
CALL FUNCTION 'ECATT_CONV_XSTRING_TO_STRING'
EXPORTING
im_xstring = lv_in
im_encoding = lv_encoding
IMPORTING
ex_string = lv_out.
ENDFORM.
FORM frm_to_xstring USING lv_in
lv_encoding
CHANGING lv_out.
DATA: lv_len TYPE i.
CALL FUNCTION 'ECATT_CONV_STRING_TO_XSTRING'
EXPORTING
im_string = lv_in
im_encoding = lv_encoding
IMPORTING
ex_xstring = lv_out
ex_len = lv_len.
ENDFORM.
FORM frm_base64encode USING lv_in
CHANGING lv_out.
CALL FUNCTION 'SCMS_BASE64_ENCODE_STR'
EXPORTING
input = lv_in
IMPORTING
output = lv_out.
ENDFORM.
FORM frm_base64decode USING lv_in
CHANGING lv_out.
CALL FUNCTION 'SCMS_BASE64_DECODE_STR'
EXPORTING
input = lv_in
unescape = 'X'
IMPORTING
output = lv_out
EXCEPTIONS
failed = 1
OTHERS = 2.
ENDFORM.This is Plaintext 这是明文 Fake News
AESEncryptionKey
5468697320697320506C61696E7465787420E8BF99E698AFE6988EE696872046616B65204E657773
414553456E6372797074696F6E4B6579
00000000000000000000000000000000CECDFF97772C03F3F7FD52C235105F5824460833D3167F5744B47DDE33565346AB37B067DC347402A0A438F6DD30F8A0
This is Plaintext 这是明文 Fake News
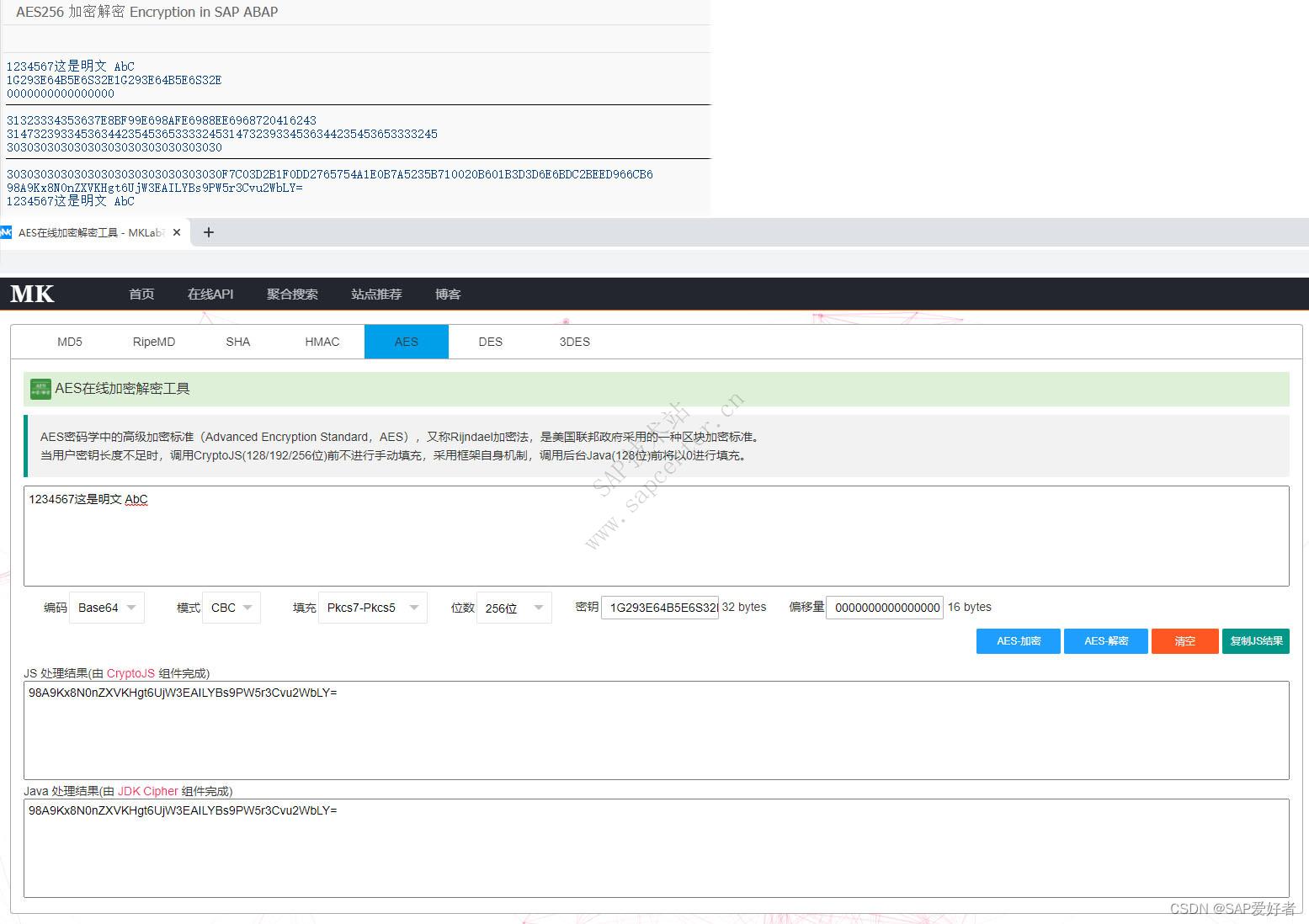
1234567这是明文 AbC
1G293E64B5E6S32E1G293E64B5E6S32E
0000000000000000
31323334353637E8BF99E698AFE6988EE6968720416243
3147323933453634423545365333324531473239334536344235453653333245
30303030303030303030303030303030
30303030303030303030303030303030F7C03D2B1F0DD2765754A1E0B7A5235B710020B601B3D3D6E6BDC2BEED966CB6
98A9Kx8N0nZXVKHgt6UjW3EAILYBs9PW5r3Cvu2WbLY=
1234567这是明文 AbC
用网上的 AES在线加密解密工具进行验证 https://www.mklab.cn/utils/aes
https://www.mklab.cn/utils/aes
文章来自于网络,如果侵犯了您的权益,请联系站长删除!



